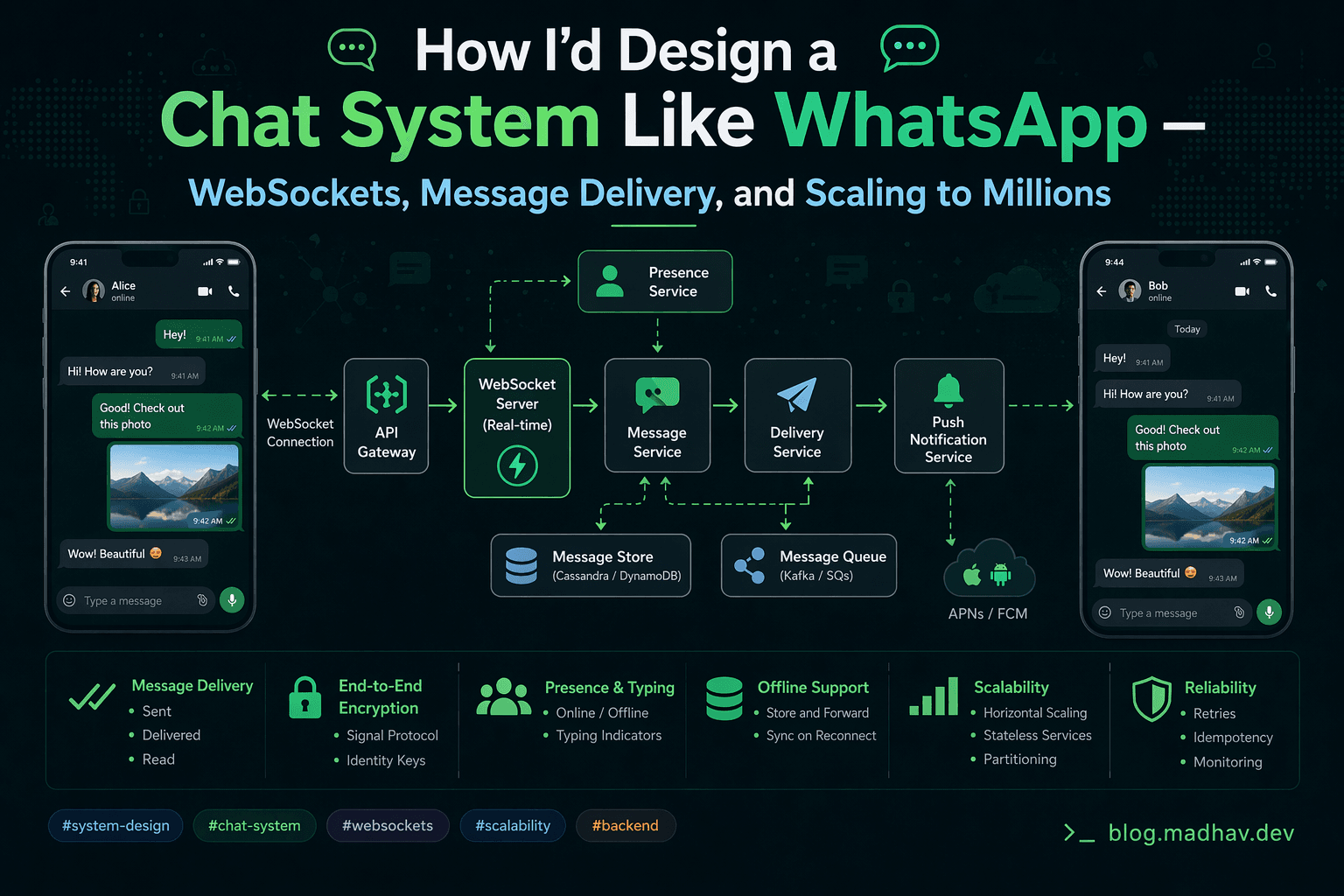
How I'd Design a Chat System Like WhatsApp — WebSockets, Message Delivery, and Scaling to Millions
A practical system design breakdown covering 1-on-1 and group messaging, delivery guarantees, and the architecture decisions that actually matter in production